This is the continuation of my earlier post My road to AWS Certified Solution Architect.
https://medium.com/@devopslearning/my-road-to-aws-certified-solution-architect-394676f15680
I wrote the AWS Certified Solution Architect exam almost 8 months back and after clearing that exam I decided to write my second AWS exam in the next three months but those three months became six. A couple of weeks back I watched the below youtube video “Inside the mind of a master procrastinator | Tim Urban” and was able to co-relate myself to this guy. That was the time when the Panic Monster hit inside my brain and told me this is the correct time to write the next exam.
YAY I cleared the exam!
WARNING: Some House Keeping task, before reading this blog 🙂 🙂
1: As everyone needs to sign NDA with AWS, I can’t tell you the exact question asked during the exam neither I have GB of memory, but I can give you the pointers what to expect in the exam.
2: As we all know AWS infrastructure updates everyday, so some of the stuff might not be relevant after a few days/weeks/months.
3: Please don’t ask for any exam dumps or question, that defeats the whole purpose of the exam.
Exam Preparation
- I highly recommend the Linux Academy Course to everyone, Adrian Cantrill did an excellent job in explaining all the concepts and going into the in-depth of all topics.
https://linuxacademy.com/course/aws-certified-security-specialty/
- My second recommendation is Acloudguru, especially there “Updates For 2019” section.
https://acloud.guru/learn/aws-certified-security-specialty
- AWS Re: Invent Videos: I highly recommend going through these videos, as they will give you enough in-depth knowledge about each service.
- AWS Documentation: Best documentation ever provided by any service provider. Don’t miss the FAQ regarding each service (especially for KMS, IAM, VPC).
Once you are done with the above preparation, it’s a good time to gauge your knowledge, check the AWS provided sample question.
Now coming back to the exam, the entire exam is divided into five main topics.
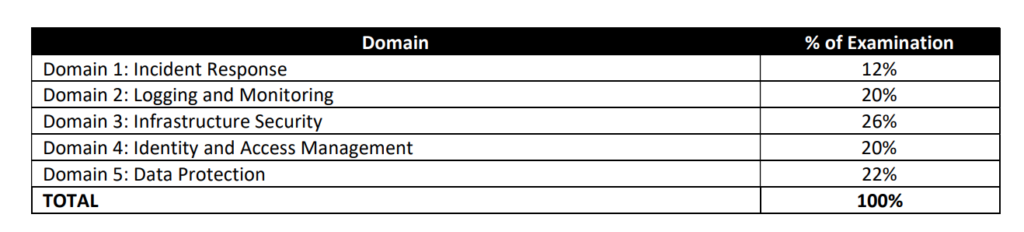
Based on my experience, you must need to know these four services to clear this exam.
- KMS
- VPC
- IAM
- Identity Federation(This is a surprise package to me, I saw almost 5–6 questions related to Identity Federation).
Domain 1: Incident Response
- What steps you will perform if your ACCESS_KEY and SECRET_ACCESS_KEY got leaked accidentally on GitHub(Tips: You need to rotate the key immediately, update your application which is using this key(good idea to use Role) and then disable/delete this key).
- What steps to follow if your EC2 instance got compromised(Tips: Take the snapshot of EBS volume, Build instance in your forensic subnet or isolate this instance).
https://aws.amazon.com/premiumsupport/knowledge-center/potential-account-compromise/
Domain2: Logging and Monitoring
CloudTrail
- Make sure you understand that same Cloudtrail can be applied to all regions, the question will trick you, do you create one trail per region or the same trail can be applied to multiple regions? What will happen to all the future region, can the same trail will be applied or do we need to create a new trail?
- Must try CloudTrail multi-account scenario(Where you can create one central S3 bucket and can push trail from different accounts)(Common issues: Not able to push logs from the particular account? Does the S3 bucket policy looks correct? Do we have an IAM Resource defined for that particular account?)
CloudWatch
- How to troubleshoot if cloud watch agent is not sending logs to CloudWatch Log Group(Some Tips: Is cloudwatch agent running? Does EC2 Instance Role have sufficient permission to push logs to CloudWatch Logs)
- Cloudwatch metrics to filter events and create an alert?(eg: Failed logins or someone trying to break-in with root credentials)
https://docs.aws.amazon.com/AmazonCloudWatch/latest/logs/ExtractBytesExample.html
VPC Flow Logs
- Must remember this point, VPC Flow Logs is not for deep packet inspection or analysis(it only hold metadata), for a deep packet inspection you need third party tool(eg: Wireshark)
- Understand the format of VPC Flow Log and check some sample flow logs(Pay special attention to ACCEPT vs REJECT field, where packets are getting REJECTED at Security Group Level or NACL)
2 123456789010 eni-abc123de 172.31.16.139 172.31.16.21 20641 22 6 20 4249 1418530010 1418530070 ACCEPT OK
2 123456789010 eni-abc123de 172.31.9.69 172.31.9.12 49761 3389 6 20 4249 1418530010 1418530070 REJECT OK
https://docs.aws.amazon.com/vpc/latest/userguide/flow-logs.html
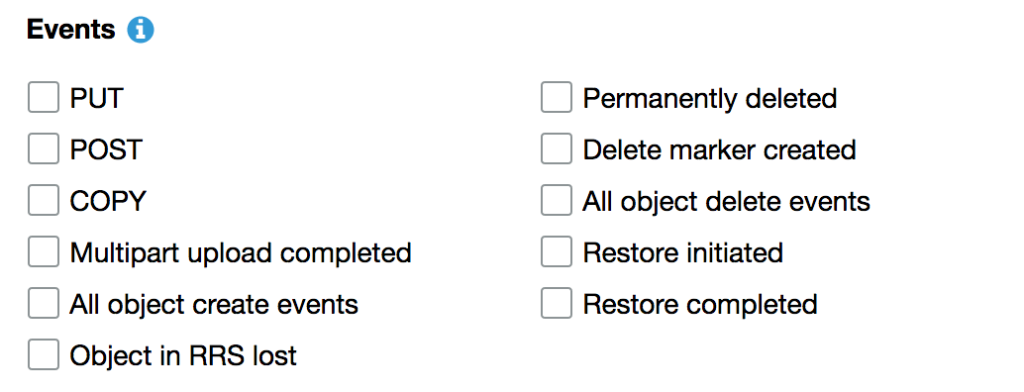
S3 Events
- Different type of S3 events
https://docs.aws.amazon.com/AmazonS3/latest/dev/NotificationHowTo.html
AWS Config
- In which cases you are going to use AWS Config? Some use cases
* Ensure that EC2 instances launched in a particular VPC are properly tagged.
* Make sure that every instance is associated with at least one security group.
* Check to make sure that port 22 is not open in any production security group.
https://aws.amazon.com/blogs/aws/aws-config-rules-dynamic-compliance-checking-for-cloud-resources/
AWS Inspector
- Understand what is the use of the inspector
https://aws.amazon.com/premiumsupport/knowledge-center/set-up-amazon-inspector/
https://docs.aws.amazon.com/inspector/latest/userguide/inspector_rule-packages.html
- What is a rule package?
A rules package is a collection of security checks that can be configured as part of an assessment template and assessment run.
Amazon Inspector has two types of rules packages, the network reachability rules package that checks for network accessibility of your Amazon EC2 instances, and host assessment rules packages that check for vulnerabilities and insecure configurations on the Amazon EC2 instance. Host assessment rules packages include Common Vulnerabilities and Exposures (CVE), Center for Internet Security (CIS) Operating System configuration benchmarks, and security best practices.
Domain 3: Infrastructure Security
CloudFront
- Try to create CloudFront Distribution and make a note of each step.
- What is the difference when you use your own SSL cert vs CloudFront Provided cert.
AWS WAF
- Use of AWS WAF
https://aws.amazon.com/waf/getting-started/
- Remember this, you can only use WAF with Amazon CloudFront and the Application Load Balancer (ALB)
- Whenever question asked for SQL injection and Cross-Site Scripting (XSS) think of WAF as a security solution
VPC
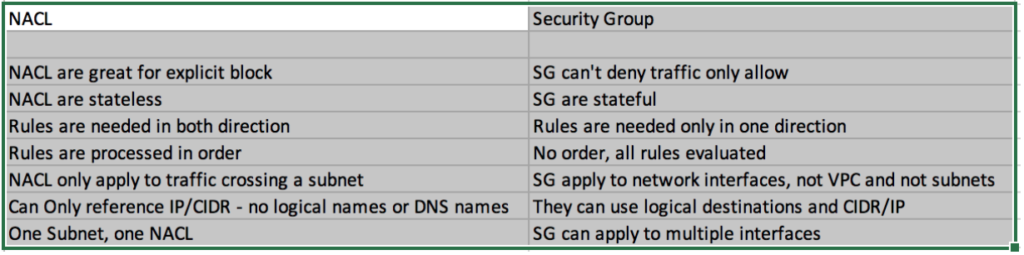
- Understand the difference between Security Group vs Network Access Control List
- VPC endpoint and check its Policies
- Example: Restricting Access to a Specific Endpoint
{
"Version": "2012-10-17",
"Id": "Policy1415115909152",
"Statement": [
{
"Sid": "Access-to-specific-VPCE-only",
"Principal": "*",
"Action": "s3:*",
"Effect": "Deny",
"Resource": ["arn:aws:s3:::my_secure_bucket",
"arn:aws:s3:::my_secure_bucket/*"],
"Condition": {
"StringNotEquals": {
"aws:sourceVpce": "vpce-1a2b3c4d"
}
}
}
]
}
https://docs.aws.amazon.com/vpc/latest/userguide/vpc-endpoints-s3.html#vpc-endpoints-policies-s3
System Manager
- Use of System Manager Parameter Store(eg: Which service you will use to store a secret in AWS, if the question is related to DB then prefer Secret Manager)
- How to use System Manager for Patching(Question could be to meet the compliance requirement you need to regularly patch your server, which AWS Service you can use)
Domain 4: Identity and Access Management
- You will see a bunch of questions related to IAM Policies and what the particular policy do?
- Make sure you are comfortable and understand the difference between IAM Policies vs Resource Policies(Especially S3 bucket policies and KMS).
- Use of AWS Organization(Remember Service Control Policy(SCP) can deny access only, they cannot allow)
- Understand how AWS Secure Token Service(STS), this is not only important for the exam but also as a part of your daily job.
Active Directory
- 5–6 questions related to active directory.
- Please brush up your concept related to Web Identity Federation and SAML.
Domain 5: Data Protection
- Must try this scenario, KMS Bring your own key.
https://aws.amazon.com/blogs/aws/new-bring-your-own-keys-with-aws-key-management-service/
- In which case you prefer HSM(look for key term like satisfying the compliance requirement)over KMS
- Understand how key Rotation works in case of AWS Managed Key(Automatically Rotated after 3 years) vs Customer Manager(Automatically rotated after 365 days — disabled by default) vs Customer Manager imported key material (No automatic rotation)
- KMS Grant: With grants, you can programmatically delegate the use of KMS customer master keys (CMKs) to other AWS principals. You can use them to allow access, but not deny it. Grants are typically used to provide temporary permissions or more granular permissions.
Other Key Topics
Macie
- Whenever question asked about PII(personally identifiable information) your best bet is Macie
Amazon Macie recognizes sensitive data such as personally identifiable information (PII) or intellectual property and provides you with dashboards and alerts that give visibility into how this data is being accessed or moved. For more info
https://docs.aws.amazon.com/macie/latest/userguide/what-is-macie.html
Athena
- When the question asked for analyzing S3 logs, then the most probable answer is Athena
Amazon S3 stores server access logs as objects in an S3 bucket. You can use Athena to quickly analyze and query S3 access logs.
https://aws.amazon.com/blogs/big-data/analyzing-data-in-s3-using-amazon-athena/
DDOS attack
- Whenever question asked about DDOS attack, then Shield might be a solution.
AWS provides two levels of protection against DDoS attacks: AWS Shield Standard and AWS Shield Advanced.
https://docs.aws.amazon.com/waf/latest/developerguide/ddos-overview.html
AWS Secret Manager
- Remember this point, when you enable the secret manager it will rotate credentials immediately. Make sure all your application instances are configured to use Secret Manager before enabling credentials rotations
https://docs.aws.amazon.com/secretsmanager/latest/userguide/intro.html
AWS SES
- Remember the port Number
- Port 25 is the default but EC2 throttles email traffic on port 25
- To avoid timeout either use port 587 or 2587
AWS Lambda
- Understand the difference between Function Policy(helpful in troubleshooting if cloud watch doesn’t get invoked) vs Lambda Execution Role(Where Lambda need to perform some action eg: Stopping any EC2 instance)
AWS Glacier Vault Lock
- Initiate the lock by attaching a vault lock policy to your vault, which sets the lock to an in-progress state and returns a lock ID. While in the in-progress state, you have 24 hours to validate your vault lock policy before the lock ID expires.
https://docs.aws.amazon.com/amazonglacier/latest/dev/vault-lock.html
AWS EBS
- Make sure you understand this part
Does Amazon wipe EBS drive data upon deletion?
Your data will live in the storage system for an indefinite period of time after you terminate the volume but will be wiped prior to being available to another user.
https://forums.aws.amazon.com/thread.jspa?threadID=111692
Final Words
- As this is the Speciality exam, you will except this exam to be much more difficult as compared to other exam and on the top of it you need to know so many aws services not just skimming through it but you need to know in-depth but in the end you will learn so much out of it. So keep calm and write this exam and let me know in case if you have any question.

Thanks for the detailed write up .
Thanks a lot for an excellent review, I just Passed AWS SAA and now preparing for Security Specialist.
These pointers will really help a lot
Hi Mathur,
Could you please provide your pointers on SAA as i am planning to sit for this exam soon.
Thanks
Sandeep
Hi Sandeep
Please check my earlier blog https://medium.com/@devopslearning/my-road-to-aws-certified-solution-architect-394676f15680
–Prashant
Hey there just wanted to give you a quick heads up and let you know a few of the pictures aren’t loading properly. I’m not sure why but I think its a linking issue. I’ve tried it in two different internet browsers and both show the same outcome.
Thanks for your feedback, Can you please let me know which one is not working, I will try to fix it.
Congratulations on your certification and thanks for sharing the info and helping the security community to grow.
Thanks Shiva